Cloud computing has revolutionized IT infrastructure by enabling scalable, on-demand services. However, it introduces...
Cyber Security
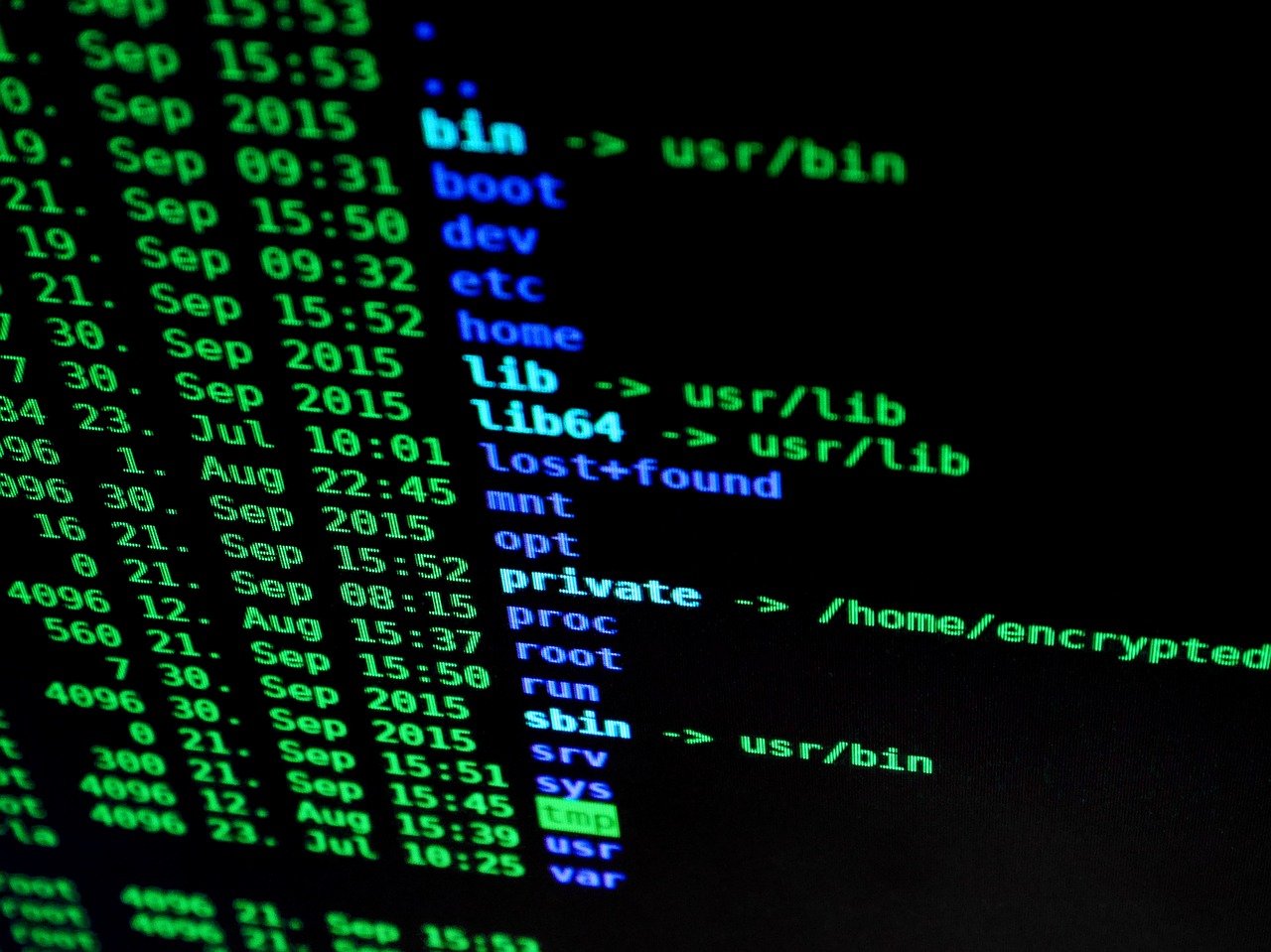
Overview In the ever-evolving digital landscape, securing web applications has become a critical necessity...
Learn how to secure your electric car from cyber attacks and theft. Our comprehensive...
What is Vulnerability Management? Vulnerability management is a process that is designed to identify,...
Introduction Micro-segmentation is a network security strategy that involves dividing a network into smaller...
Your data is important. Whether you're a business owner or just someone with...
Are you looking for the best intrusion prevention systems to keep your network safe?...
Routers are the central hub for all of your home’s internet-connected devices including...
A Web Application Firewall (WAF) is an application firewall that protects the servers...
A firewall is a computer security system that monitors and controls the incoming...
A firewall is a computer security system that monitors and controls the incoming...
In the modern world, a firewall is a must-have for every computer that can...
This article is all about Next-generation firewalls. They are the best way to...
Firewall will likely contain the current major network security threats, how to protect against...
Network Segmentation is performed by separating network traffic into multiple network segments, allowing...
Firewalls are designed to control the flow of packets between networks, which means...
Today we're going to discuss types of firewalls and how they work. Pay...
In the modern age, office and home are two things that have become one....
There are network security control devices that facilitate filtering and routing of data in...